Picture this: You wake up to find an email from your bank, urgently requesting your login details due to a supposed security breach. Alarming, right? Yet, such emails, despite seeming legitimacy, might be fraudulent attempts aiming to dupe unsuspecting recipients into divulging sensitive information. Enter the trio of email authentication protocols: SPF, DKIM, and DMARC. These ensure that the emails landing in your inbox are the real deal, not sneaky imposters trying to cause trouble. Email authentication might sound technical but think of it as a special lock or shield that keeps your emails safe and trustworthy. For businesses that use email a lot, it is like a handshake that assures recipients that the email that they are reading is genuine.
SPF: Sender Policy Network
SPF is like a bouncer for your email inbox. It also determines which servers are authorized to send emails on behalf of a domain. SPF works by publishing a specific list of authorized email servers in the DNS (Domain Name System) records of a domain.
Here is the SPF record published by Reddit as an example:
This implies that your inbox should receive emails from @reddit.com addresses only if they were sent from servers at amazonses.com, google.com, mailgun.org, hubspotemail.net, and those particular IP addresses listed as approved servers within the DNS records. When an email arrives, SPF validation kicks in. It checks if the sending server matches the designated records. If the server's identity aligns with the records, the email is more likely to get through. If not, it might be marked as suspicious or even get rejected.
DKIM: Seal of Approval
DKIM, or DomainKeys Identified Mail, is similar to affixing a digital seal to your emails. It operates by adding an encrypted signature to the email's header using a private key. The corresponding public key, residing in the domain's DNS records, allows the recipient's email provider to verify the email's authenticity. This cryptographic signature acts a tamper-proof seal, ensuring the email's content remains unaltered throughout its journey.
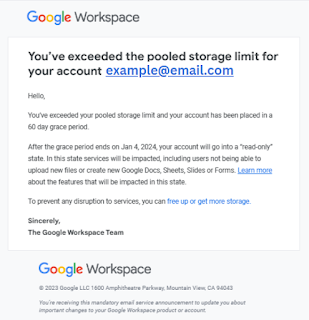
Emails like this often appear in spam folder, prompting a cautionary approach due to suspicious origins.
Deep diving into the mail specifics,
'Mailed-by' refers to the sender's domain. If the correct domain appears here, it means the email passed SPF authentication.
'Signed-by' showcases a sample DKIM. However, in this example, the sender used a generic Google DKIM signature, hence the different signed-by domain. Using a generic DKIM signature signifies absence of a customized DKIM setup. This situation often leads to the email being flagged or marked as suspicious.
The importance of setting up DKIM is to establish email's authenticity. If the domain implements a custom DKIM, the 'signed-by' domain will display the same domain as in the "from" address, increasing the email's credibility.
DMARC: Orchestrating Email Security
DMARC stands for Domain-based Message Authentication, Reporting, and Conformance. It is an email authentication protocol that helps prevent email spoofing and phishing by allowing domain owners to specify how their emails should be authenticated.
DMARC works right after confirming authentication with SPF and/or DKIM. If the answer is yes, the next step DMARC will do is domain alignment. Domain alignment ensures that the domain used in the "From" address of the email aligns with the actual domain that sent the email. It checks two things: SOF, which confirms the sender's server, and DKIM, which adds a digital signature to the email. If alignment is successful, it enhances email security, making it harder for malicious actors to impersonate legitimate senders. If alignment fails, DMARC policies can instruct receiving mail servers on how to handle these unauthenticated emails, reducing the risk of phishing and spoofing attacks.
SPF, DKIM, and DMARC in Harmony
When harmoniously implemented, SPF, DKIM, and DMARC form an impenetrable shield against email spoofing and phishing. Their collaborative efforts not only bolster email security but also enhance deliverability, enduring legitimate emails reach their intended recipients' boxes rather than the dreaded spam folders or worse, be rejected.